Data Processing Agreement

Last updated: January 13, 2026
Synthesia offers a Data Processing Addendum that supplements the Customer Terms of Service or any main online subscription agreement. This addendum reflects our requirements as a processor of Customer Data. Please have an authorized individual execute this agreement using the link below.
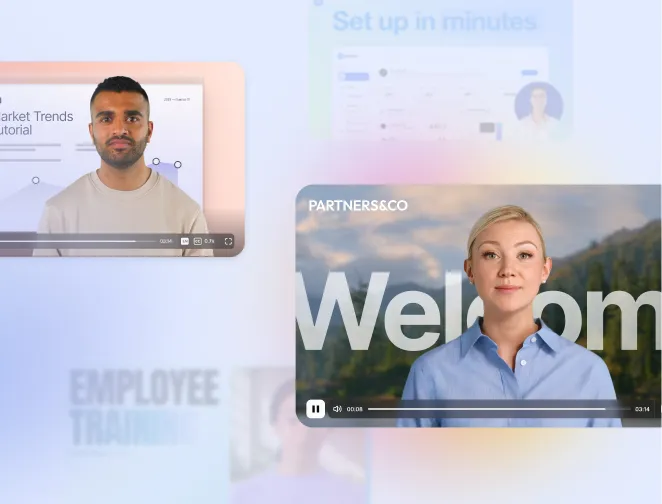
Recommended videos
Need more help?
If you need assistance with Synthesia or have a question about our products or services, please contact our customer support team.
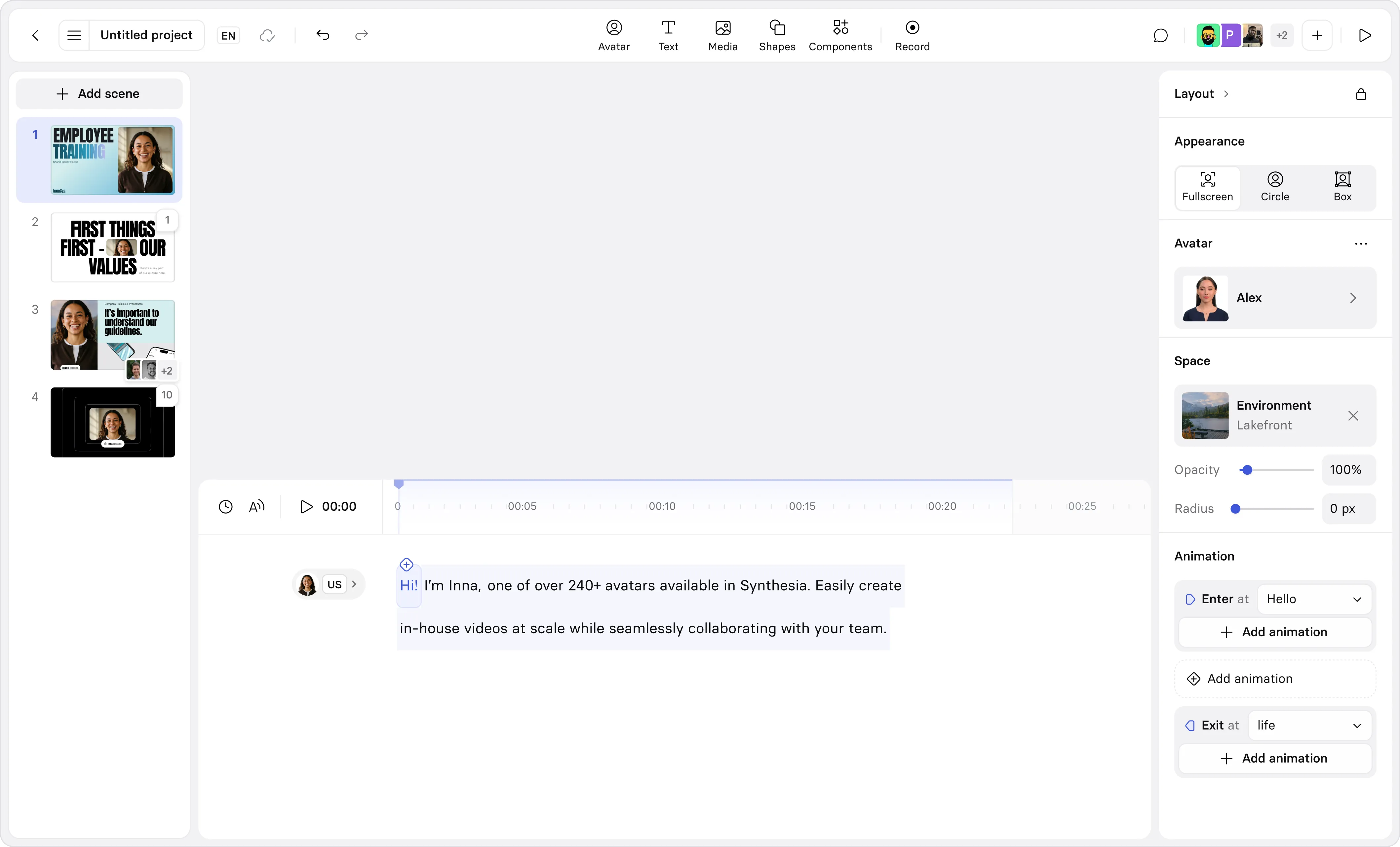
Try Synthesia with a free video.
Simply type in text and get a free video with an AI avatar in a few clicks. No signup or credit card required.
Create free AI Video